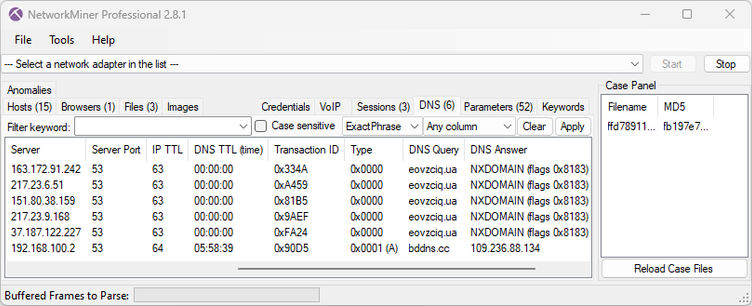
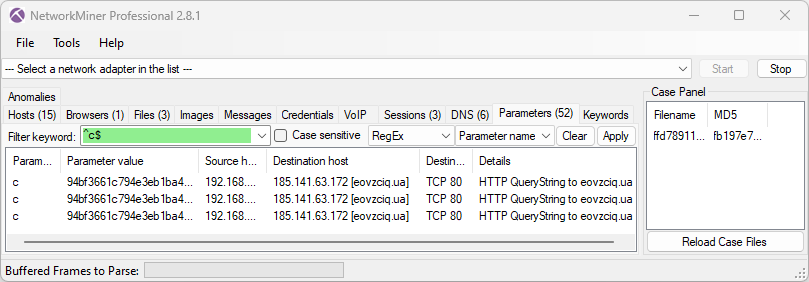
Here’s an example where the bot attempts to resolve the C2 hostname using all the hard coded name servers, but fails. It then falls back to querying bddns[.]cc over HTTP to resolve the IP address of the C2 server, which works out. The second screenshot shows the bot's c=94bf3661c794e3eb1ba4 checkin command.
The PCAP is from an execution of a malicious EXE (MD5 55a14f9e05962654f774b8129ec4c2ca) on any.run.
Most AV vendors label this malware as #zusy, #ekstak or #staser