A Gaggle of Boards Makes For an I2C Playground
It's not much of a stretch to assume that the majority of Hackaday readers are at least familiar with I2C. In fact, there's an excellent chance that anyone who's ever done more with an Arduino than blink the onboard LED has at one time or another used the serial communication protocol to talk to a sensor, display, or other external gadget. Of course, just because most of us have used it in a few projects doesn't mean we truly understand it.
If you're looking to brush up on your I2C knowledge, you could do worse than to follow the guide [András Tevesz] recently wrote up. With a title like Hardware Hacking 101: E01 I2C Sniffing, How to Listen to Your Arduino 's I2C Bus, you know you're in for a good time. While the document is arguably geared more towards security researchers than electronic hobbyists, the concepts presented can be useful even if you're just trying to debug your own projects.
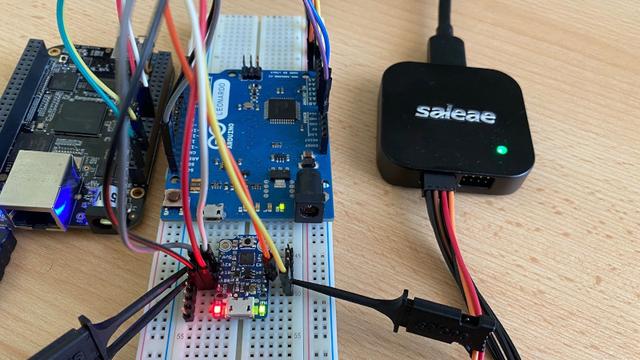
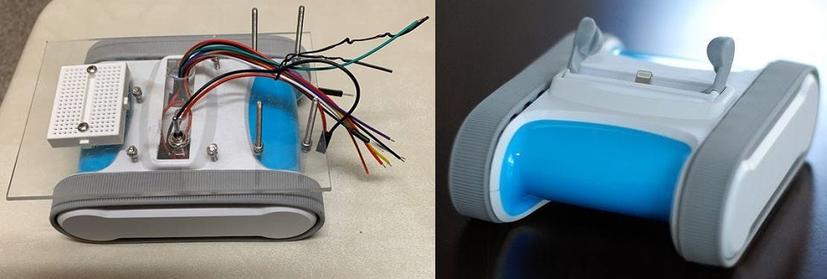
While you could certainly adjust the hardware used to fit whatever you've got kicking around the parts bin, the setup [András] details uses a BeagleBone Black as the master device that communicates with an Adafruit Trinket and Arduino over I2C. He provides code for all three devices, and when everything is running as it should be, the microcontrollers will blink their LEDs in time with signals being sent out over the bus by the BeagleBone.
This, in itself, has educational value. Sure most of us have used turn-key I2C devices, but how many have actually made one? But beyond that, it also gives you a simple and user-controllable bus to poke around in. [András] hooks up a Saleae logic analyzer (never fear, that $10 USD one you got on eBay will work just as well) and studies the actual messages as they go over the wire. If you've ever wanted to take a close look at the nuts and bolts of this ubiquitous protocol, it's a great way to get your foot in the door. While on the subject, be sure to check out the excellent guide our own [Elliot Williams] wrote up back in 2016.
[Thanks to zh4ck for the tip.]
#parts #softwarehacks #i2c #logicanalyser #serialcommunications #sniffing