Protect your Linux servers in 2026! This essential guide covers SSH key authentication, firewall configuration, automated patching, and least privilege access best practices. A must-read for sysadmins and security-conscious users. #LinuxSecurity #ServerHardening #SSH #Firewall #SysAdmin https://estoreab.com/linux-server-security-best-practices
Looking to strengthen your Linux server security? Our comprehensive guide explores 10 essential hardening techniques for 2026, from SSH keys to automated patching. #LinuxSecurity #ServerHardening #Cybersecurity #LinuxAdmin https://estoreab.com/linux-security-hardening-guide
Looking to fortify your Linux server as we approach 2026? Our new guide covers essential security hardening techniques including SSH key authentication, firewall configuration, kernel hardening, and automated patching. A must-read for system administrators and security-conscious users! #LinuxSecurity #ServerHardening #CyberSecurity #LinuxAdmin #InfoSec https://estoreab.com/linux-security-hardening-guide
Wondering how to keep your Linux servers secure in 2026? 🖥️ Check out this comprehensive guide covering SSH hardening, Fail2Ban setups, and kernel live-patching. Essential for sysadmins! #LinuxSecurity #SSH #Fail2Ban #SysAdmin #LinuxTips https://estoreab.com/linux-security-roadmap-2026
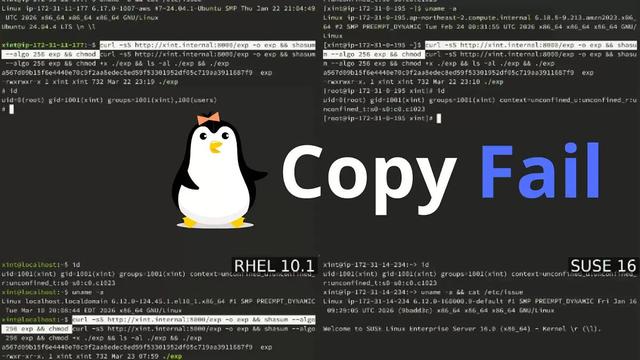
Copy Fail (CVE-2026-31431) is a 4-byte write into the Linux page cache that hands root to any local user in seconds. No race, no ASLR bypass, a 2017 "in-place is faster" optimization in algif_aead, exploitable in 2026 with 732 bytes of Python.
The boundaries that hold are the ones that don't share a kernel: Firecracker, V8 isolates, gVisor. Shared-kernel containers, you have homework.
#LinuxSecurity #KernelSecurity #DevOps
Copy Fail Linux Privilege
Copy Fail is a Linux kernel privilege escalation flaw. Learn who may be affected, why it matters, and how to update safely.Dirtyfrag: Universal Linux LPE
https://www.openwall.com/lists/oss-security/2026/05/07/8
#HackerNews #Dirtyfrag #UniversalLinux #LPE #LinuxSecurity #Exploit #Vulnerability #OpenSource
CopyFail (CVE-2026-31431) is a high-severity Linux kernel vulnerability -- patches are out now for Rocky Linux 8.10, 9.8, and 10.1.
Any unprivileged local user can escalate to root in seconds. Multi-tenant hosts, containers, and CI runners should prioritize this one.
Fix it with:
sudo dnf --refresh update 'kernel*'
Full write-up on the blog:
https://forums.rockylinux.org/t/copyfail-cve-2026-31431-patches-now-available-for-rocky-linux/20422
#RockyLinux #Linux #OpenSource #LinuxSecurity #CopyFail
CopyFail (CVE-2026-31431): Patches Now Available for Rocky Linux
TL;DR: A high-severity local privilege escalation vulnerability in the Linux kernel has been publicly disclosed with a working exploit. Patches are available now for Rocky Linux 8.10, 9.7, and 10.1. Update your kernel and reboot. What happened On April 29, security researchers from Theori disclosed a Linux kernel vulnerability they named CopyFail, tracked as CVE-2026-31431. The flaw has been present in essentially every mainstream Linux kernel built since 2017. The bug sits in the kernel’s alg...
Aggregated from www.darkreading.com.Read the full article →
https://sudoaptchat.com/gisec-global-2026-the-middle-east-amp-africas-largest-cybersecurity-event/
#LinuxSecurity