You know why I love computer security?
This is why.
A big corpo fuck you up? Fuck them back.
While other field is just staggering with "uh, we need to do abcdefg first to make right what is in front of us"
Context: Security researcher are now contacting NightmareEclipse, and willingly to drop Windows product zero days they found in the name of solidarity.
#computersecurity #infosec #cybersec #activism #windows #zeroday
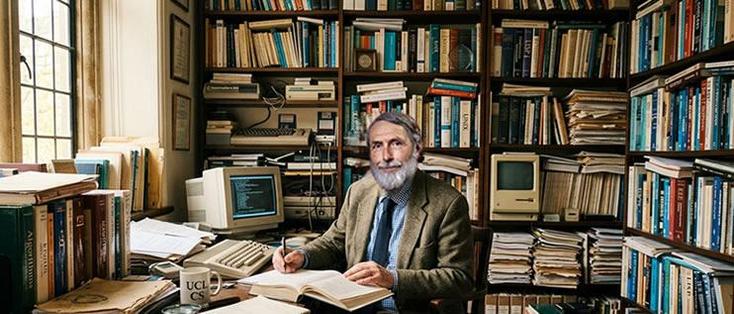
Peter G. Neumann, Computer Security Pioneer, Dies at 93
Computer security pioneer Peter G. Neumann, who warned about digital risks for decades, has died at 93. His work focused on safety and privacy.
#ComputerSecurity, #PeterNeumann, #TechPioneer, #DigitalRisks, #RIP
https://newsletter.tf/computer-security-expert-peter-neumann-dies-93/
Peter G. Neumann, a key figure in computer security, has passed away at 93. He spent his career highlighting risks in digital systems.
#ComputerSecurity, #PeterNeumann, #TechPioneer, #DigitalRisks, #RIP
https://newsletter.tf/computer-security-expert-peter-neumann-dies-93/

Computer Security Expert Peter Neumann Dies at 93 in California
Computer scientist Peter G. Neumann, who warned about digital dangers, died Sunday, May 17, 2026, in Santa Clara, California, at age 93.
In Memoriam: Peter G. Neumann
Met het overlijden van Peter G. Neumann op 93-jarige leeftijd verliest de technologiewereld een van zijn meest visionaire en standvastige pioniers. Dr. Neumann overleed in Californië aan de gevolgen van een val. Sinds 1971 was Neumann als computerwetenschapper verbonden aan SRI International. […]
https://cloudzeeland.nl/in-memoriam-peter-g-neumann/#InMemoriam #PeterGNeumann #ComputerSecurity #Privacy #CheriAlliance #Informatica #TechPionierWe're meeting tonight! Friday 1st May at #Glasgow #hackerspace - @thegamerclub at 153 Bath Lane from 6pm 'til late - all welcome!
Hackers, crackers, geeks, hats of any colour, technology enthusiasts, hacktivists, and other like-minded folks are most welcome. We do not judge anyone and everyone has something to contribute, no matter their level of expertise!
Also join us in Matrix at #2600:glasgow.social (invite link: https://glasgow.social/matrix)
#infosec #hacker #computersecurity
You're invited to talk on Matrix
You're invited to talk on Matrix
🎉 #EuroSec2026 has wrapped up in Edinburgh 🇬🇧!
We closed the 19th European Workshop on Systems Security with an amazing keynote by Lorenzo Cavallaro — a fantastic finale to a day filled with insightful talks, engaging discussions, and vibrant community interaction.
Thank you to all speakers, authors, and participants who made it such a great event!
#EuroSys2026 #SystemsSecurity #InfoSec #ComputerSecurity
🎉 #EuroSec2026 is underway in Edinburgh 🇬🇧!
We kicked off the 19th European Workshop on Systems Security with a warm welcome from our Program Chair Andrea Continella and an engaging keynote by Kaveh Razavi that set the tone for a fantastic day.
Looking forward to great discussions, talks, and community interactions!
#EuroSys2026 #InfoSec #SystemsSecurity #ComputerSecurity
The thing about computer security is that while it is by no means absolute, that doesn't mean it's pointless. In the same way it's not pointless to avoid posting your credit card number online just because people can still steal it if you don't, it's not pointless to avoid revealing other information about yourself just because there are people who can find that information through other means.
In fact it is a general principle that perfect security is impossible, whether online or offline. Increased security can sometimes also come at unacceptable cost, not just in money, but time, convenience, and social connection. So good security is about finding good tradeoffs, and what may be acceptable to one person may not be to another.
But learning about security can help you figure out whether it's worthwhile to change your security practices.