Anthropic Unveils Claude Security for AI-Powered Vulnerability Scanning
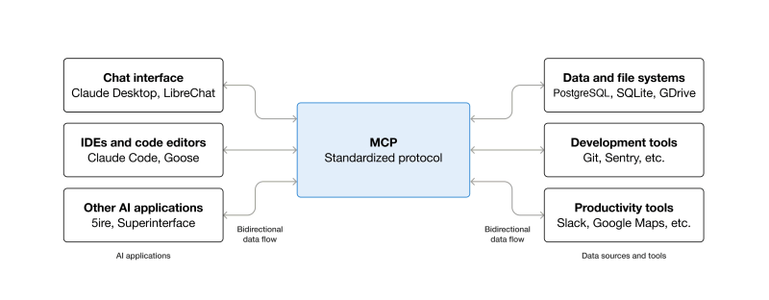
Boost your organization's security with Claude Security, now in public beta, which scans codebases to detect and fix software vulnerabilities with just a few clicks. Say goodbye to tedious API integrations and custom agent builds - simply access the feature from the Claude.ai sidebar and start…
#AipoweredVulnerabilityScanning #ClaudeSecurity #VulnerabilityManagement #CodeSecurity #EmergingThreats