✨ Deceiving Windows Defender: The Big Stack Bypass
👉 Creating a large (>2MB) payload allocated on the stack
👉 Move the payload inside of main, and front load it with NOPs
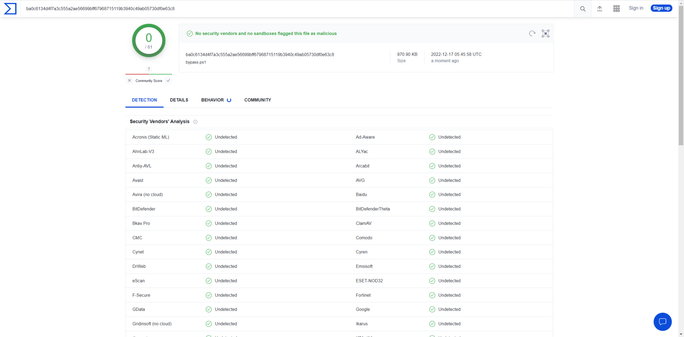
👉 Could break a lot of automated analysis
https://steve-s.gitbook.io/0xtriboulet/deceiving-defender/deceiving-defender-the-big-stack-bypass