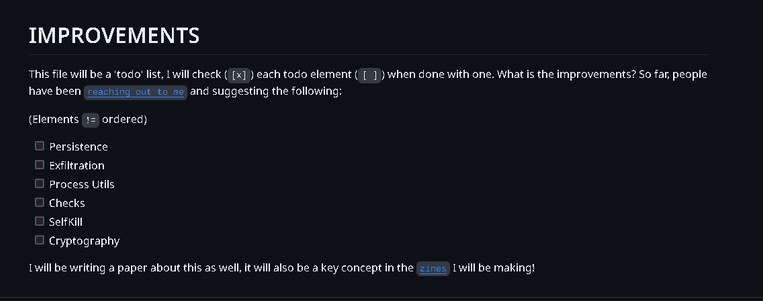
The Reverse Shells I am making (or, should I rather say "Improving") is going to be more "useful" in the future, namely the following "plugins" will be able to be loaded on compile time.
Some have been sending me a few tips on what I can improve my RevShells to; and the below have been chosen to at least been looked into
(basically, I will look into each of the bellow points) I chose these because they were "generally useful" rather than something very specific (and, because of that, only 'useful' to a smaller audience)
- Cryptography (everything is now in plain text, so I wanted to add a cryptography addon , both for the file itself but also for the actual communication(s))
- SelfKill date (this is pretty self explanatory)
- Checks (IsDebuggerPresent, Etc, Am I running with highest elevation, and so on and so forth)
- Is the network connected? How is the delay?
- Process Utils (read and write memory on other processes) (Like, read "ABC" in process(es) "notepad*.exe" and replace "ABC" with "XYZ") <- this will be a work in progress, and be handled last.
- Persistence (The Cliche 'StartUp')
- Backdoor (USB mainly inspired from StuXnet and Fanny.bmp)
- Presence Altering(Hiding, decoy proc names, etc)
- Exfiltration ( Data, Reg, Etc. )
Peace out! 
One Bonus thing, if I feel for it, and if it gets popular enough, ill try to make a driver and merge with the rev shell too, and include instructions on how to compile and use. The reason here being I would want it to be able to be both*
* user and kernel mode (broadly speaking, now this does not really have any deeper definition)
https://github.com/loneicewolf/ReverseShells
#securitytools
#cprogramming #programming #revshell #reverseengineering #githubproject #github #infosec #malware