Model-based digital twin engin...
Model-based digital twin engin...
SMOKE2.0 whitebox anonymizatio...
SMOKE2.0 whitebox anonymization of sensitive information in Simulink with structure preservation - Software and Systems Modeling
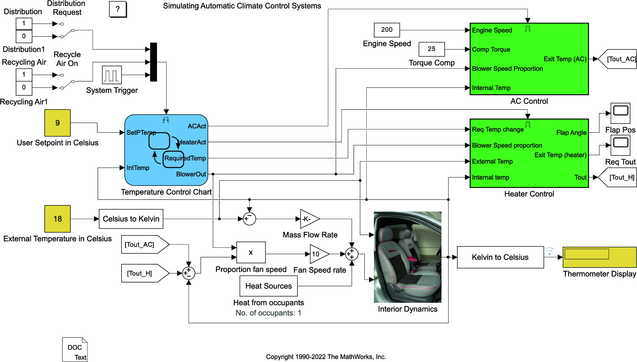
Simulink is widely used across various industries to model and simulate cyber-physical systems. Most industry-built models contain sensitive information, which prevents companies from sharing models with interested third parties, such as researchers or collaborating companies. However, advancing model-based engineering research requires access to such models—either to derive empirical insights or to evaluate new tools. While initiatives to replace industry-built models with open-source alternatives exist, they offer only a limited remedy. In this work, we present a novel approach with Smoke, a Simulink anonymization tool designed to selectively remove sensitive information within models. This allows companies to share relevant parts of their models with researchers or other third parties while safeguarding all sensitive information. Smoke’s whitebox design preserves the model’s original format and structure, ensuring that meaningful insights remain accessible. We evaluated the tool on an extensive set of open-source models and found it successfully removes sensitive information, while preserving model structure. A video demonstration of Smoke is available online at https://youtu.be/0i42BzgJAUA .
Unlocking the power of environ...
A conversational tool for AI-d...
A conversational tool for AI-driven feedback for UML modeling - Software and Systems Modeling
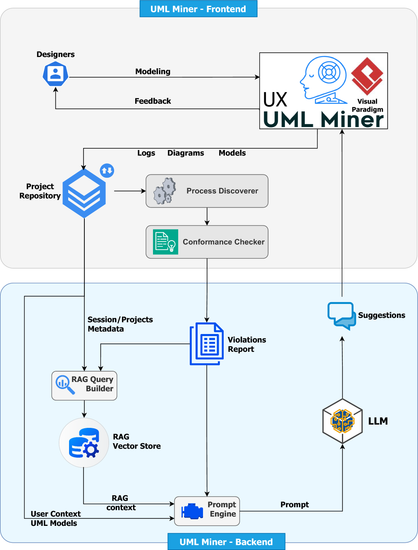
Teaching the unified modeling language (UML) is a critical task that can benefit from emerging artificial intelligence-based solutions. This paper presents UML Miner, a visual paradigm plugin designed to support the teaching and learning of UML by capturing and analyzing students’ modeling activities to deliver personalized, context-aware feedback. The tool records fine-grained software modeling actions, storing them in an event log. For each diagram, a natural language description and its XML representation are stored separately. Modeling behavior is reconstructed through process mining techniques and compared with a reference model created by the instructor using conformance checking. This analysis adopts a declarative approach, leveraging the declare language to specify behavioral constraints without enforcing a rigid action sequence, thereby accommodating multiple valid modeling strategies while preserving semantic rigor. The detected violations, together with the diagram’s natural language and XML representations, are integrated into a retrieval-augmented generation-enabled large language model, which combines accumulated knowledge with the discovered process constraints to generate enriched, pedagogically meaningful feedback in real time. An exploratory case study conducted in a real-world learning scenario evaluates the tool’s performance from both qualitative and quantitative perspectives, demonstrating its potential to improve learning outcomes and student engagement.
Model-based software sustainab...
Model-based software sustainability analysis and improvement - Software and Systems Modeling
The environmental sustainability of software has become a significant issue for the use of computing technologies. The pervasive use of software applications throughout society has potential negative environmental impacts due to the energy used by software execution, and the resulting greenhouse gas (GHG) emissions. In this paper, we describe techniques for the identification of software energy use flaws at the software modelling level, and we define techniques for the removal of such flaws via refactoring or the use of alternative specification/design modelling elements. The key idea is that energy use flaws are corrected once at the software modelling level, in order to obtain energy-efficient benefits across all target platforms. We provide a detailed evaluation to show that the proposed improvements do result in reduced energy use across multiple implementation languages and platforms. The outcome represents a novel approach for software sustainability using software models, incorporated into an established toolset for model-driven engineering.
RATEN: an efficient robustness...
Multi-Robot system environment...
Dependency-aware model repair:...
Function-driven cyber-physical...
Function-driven cyber-physical security in smart manufacturing - Software and Systems Modeling
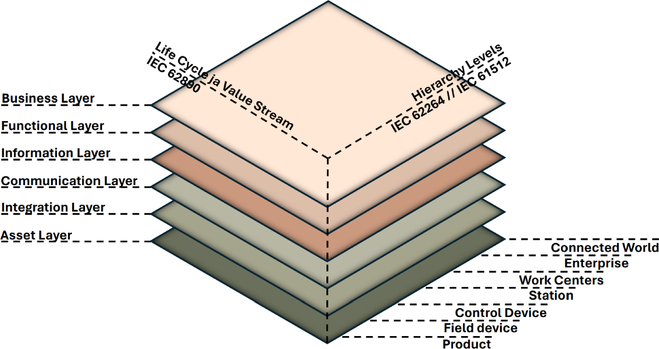
As manufacturing evolves with cyber-physical systems (CPSs), ensuring security across all components—no matter how small—is critical to preventing system-wide failures. While frameworks like Reference Architectural Model Industrie 4.0 (RAMI 4.0) structure industrial processes, they overlook security, leaving CPS vulnerable to cyber-physical threats. The increasing convergence of Information Technology and Operational Technology has further expanded the attack surface, exposing industrial automation to new vulnerabilities. This study investigates how security risks in automated manufacturing systems can be managed. Our study systematically reviews the literature, employing Information System Security Risk Management-based risk assessment and threat analysis to identify gaps in existing security frameworks. To bridge these gaps, we introduce the functions, assets, security threats, and mitigation techniques (FAST) method for assessing and mitigating security risks in CPS-driven manufacturing. Our findings highlight underexplored vulnerabilities across RAMI 4.0 layers, emphasising the need for security frameworks tailored to industrial automation. The FAST method provides a structured and scalable way to CPS security, ensuring that security measures integrate seamlessly with industrial operations while addressing previously overlooked vulnerabilities.
Enterprise modeling for the ci...
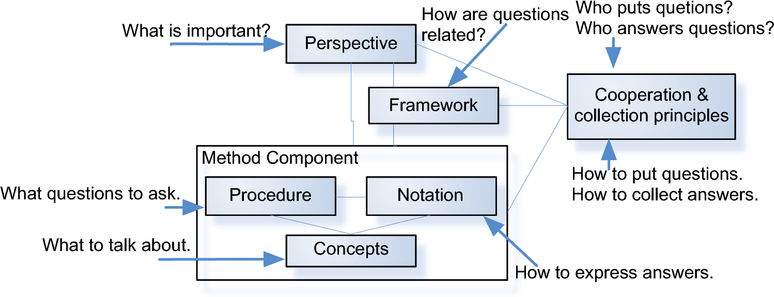
Enterprise modeling for the circular economy: meta-model and method component to support manufacturing enterprises - Software and Systems Modeling
The circular economy (CE) is an economic philosophy aimed at eliminating waste and the continual use of resources. It emphasizes designing products for longevity, reuse, and recycling to create a closed-loop system. One of the goals of enterprise modeling (EM) is to support enterprises in change processes from the current situation into a desired future state. In the context of the transition to the CE, the question arises if and how EM methods and languages must be adapted for the CE. The main contributions of this work are a better understanding of the challenges manufacturing enterprises face when preparing their product architectures for the CE, a meta-model preparing the product perspective in EM methods for CE, a QFD-based method component guiding the translation of CE goals to product properties and modules, and an investigation of what changes are required in EM methods. The work uses real-world case studies to motivate the research, identify requirements, and evaluate the findings.