🔥The "Kim" leak is an intelligence goldmine.
For analysts: We’ve got an unprecedented look into a DPRK threat actor's playbook. This isn't just about known tactics like credential theft and phishing. Our analysis shows a strategic pivot to include Taiwanese developer and government networks, revealing a clear geographical expansion of North Korea's cyber interests.
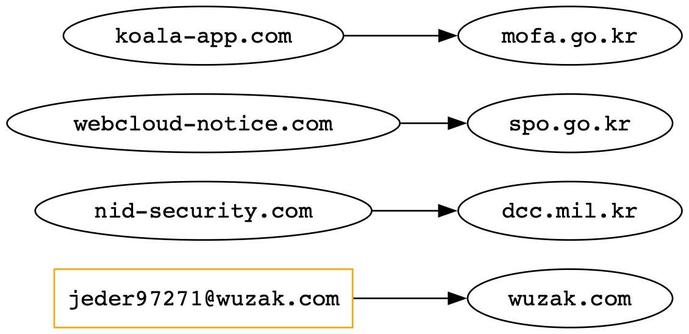
For defenders: We've mapped the full scope of this threat—from custom Linux rootkits to particular targets like PKI infrastructure and specific tools like NASM and ocrmypdf. Our report provides defensive recommendations and specific Indicators of Compromise (IOCs), so your team can detect and block this persistent, infrastructure-centric campaign.
Get the full technical breakdown and all the IOCs in our new post.
#ThreatIntelligence #Cybersecurity #NationStateAPT #Kimsuky #ThreatAnalysis #DFIR #InfoSec