Ransomware Groups Clash in Turf War, Exposing Each Other's Operations
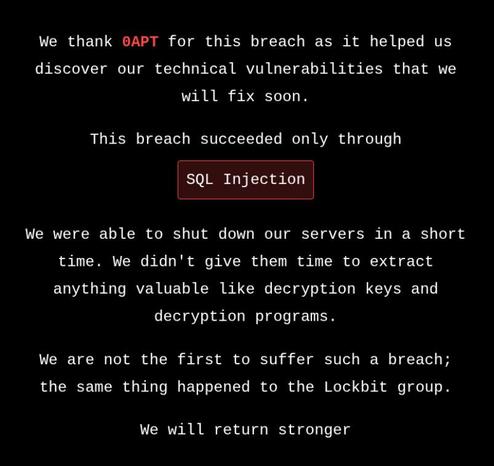
In a shocking display of cyber turf warfare, ransomware groups are clashing and exposing each other's operations, with one group, KryBit, firing back at 0APT with a defiant message. The online battle began when 0APT claimed to have taken down three rival groups, but its boasts only sparked a retaliatory strike.