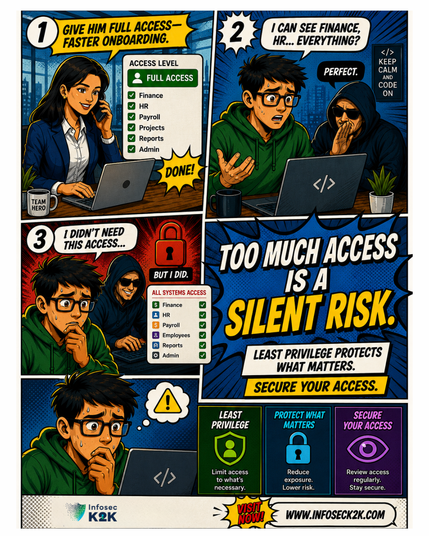
Too much access creates real risk. Infosec K2K helps secure IAM with least privilege, governance, continuous control, and better visibility across every account and system.
Reduce access risk → https://zurl.co/c9IYO
https://allthingsopen.org/articles/detecting-vulnerabilities-public-helm-charts
#k8s #kubernetes #k3s #trivytool #security #LeastPrivilege #vulnerability

Detecting vulnerabilities in public Helm charts | We Love Open Source • All Things Open
Learn how to detect security risks in public Helm charts using open source tools like Trivy, GitHub Search, and OPA. This technical guide covers misconfigurations, hardcoded secrets, and vulnerable dependencies found in widely used Kubernetes packages.
🔐 Cyber Tip: Limit admin rights. Not every employee needs elevated access.
The more admin accounts you have, the bigger your risk. Apply least privilege and review permissions regularly.
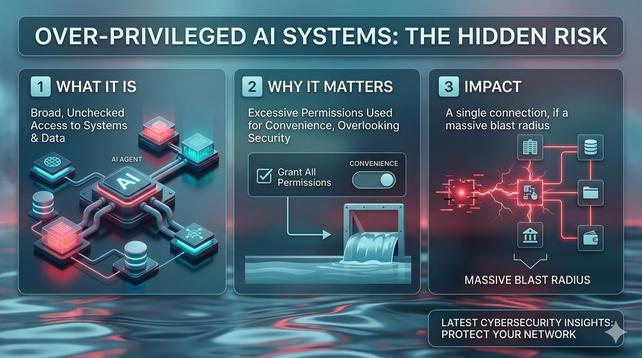
https://youtu.be/SFvZ_KjjAPA #AIsecurity #CyberSecurity #ArtificialIntelligence #AIrisks #AgenticAI #ZeroTrust #LeastPrivilege #AccessControl #InfoSec #CyberRisk #DataSecurity #EnterpriseSecurity #AIgovernance #SecurityLeadership
Daily work and system maintenance are separated into different user roles, reducing exposure if any everyday application becomes compromised.
#Kicksecure #SysmaintSplit #SecureAdmin #LinuxHardening #LeastPrivilege
📂 Limit who can access your shared files and folders.
✅ Apply least privilege—only grant access when it’s absolutely needed.
👉 https://zurl.co/sTKHH
How do you implement a least privilege access model strategy across different environments? In this article, we’ll look at how to implement and enforce least privilege across Windows, Linux, and macOS, and how to automate audits and compliance checks using PowerShell, Bash, and Ansible.
#IAM #leastPrivilege #windows #linux #macOS #PowerShell #bash #Ansible #automation #security
https://negativepid.blog/iam-designing-a-least-privilege-model/
https://negativepid.blog/iam-designing-a-least-privilege-model/
Kicksecure enforces strict privilege separation so daily activities stay isolated from administrative control, reducing system-wide risk.
#Kicksecure #UserAccountSeparation #LeastPrivilege #LinuxSecurity #SecureOperations