Importance of Multi-Layer Protection in #DDoS Mitigation
This article discusses the importance of multi-layer protection in DDoS mitigation.
Importance of Multi-Layer Protection in DDoS Mitigation
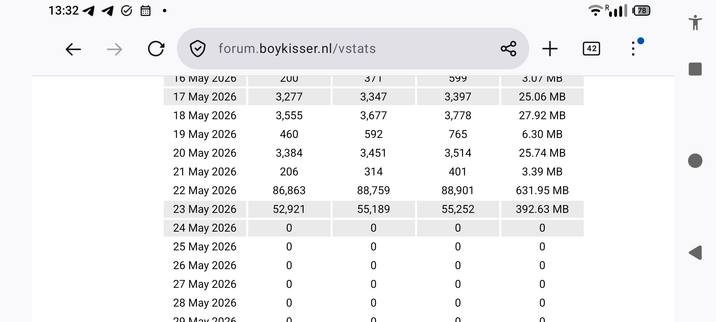
DDoS (Distributed Denial of Service) attacks can target different layers of the OSI model. A multi-layered protection approach ensures that your infrastructure is resilient against various attack vectors, particularly Layer 3 ...
Continued 👉 https://blog.radwebhosting.com/importance-of-multi-layer-protection-in-ddos-mitigation/?utm_source=mastodon&utm_medium=social&utm_campaign=mastodon.raddemo.host #security #ddosprotection