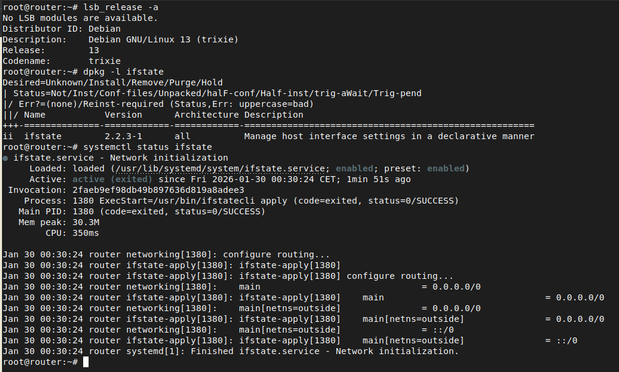
ifstate 2.3.0 - a tool for declarative network configuration for Linux - was released:
https://codeberg.org/routerkit/ifstate/releases/tag/2.3.0
This is release contains various new features like:
- bridge: VLAN membership for bridge ports
- link: support external created veth ifaces
- routing: ignore routes by ifname regex
- tc: add vlan action (allows remapping); improve change detection
The new release is already available in #AlpineLinux and in the RouterKit Debian package repository.
2.3.0 - routerkit/ifstate
## Changes - bridge: implement VLAN filtering and per-port membership (#157) - brvlan: support self-mode entries on bridge devices (#179) - fdb: add `vlan` attribute support for vlan aware bridges (#167) - hooks: make timeout configurable (#178) - link: support external created veth interf...