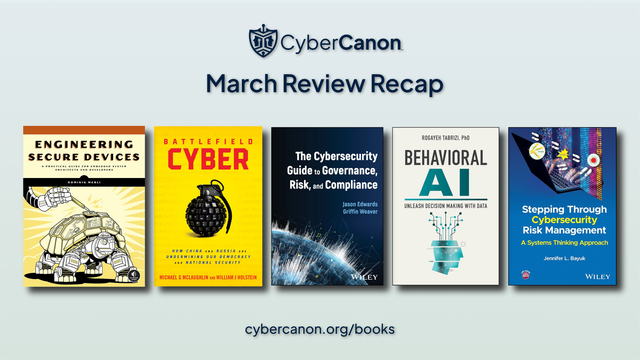
We had another strong month of reviews! Did you catch them all?
If not, we are here for you...
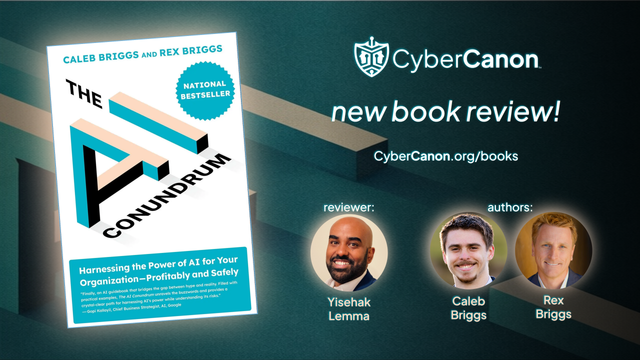
🦾 𝙏𝙝𝙚 𝘼𝙄 𝘾𝙤𝙣𝙪𝙣𝙙𝙧𝙪𝙢
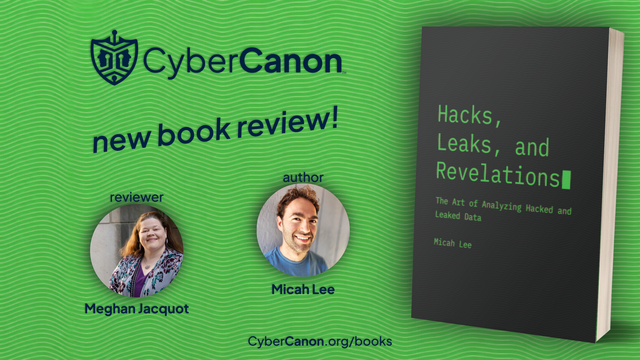
🔓 𝙃𝙖𝙘𝙠, 𝙇𝙚𝙖𝙠𝙨, 𝙖𝙣𝙙 𝙍𝙚𝙫𝙚𝙡𝙖𝙩𝙞𝙤𝙣𝙨
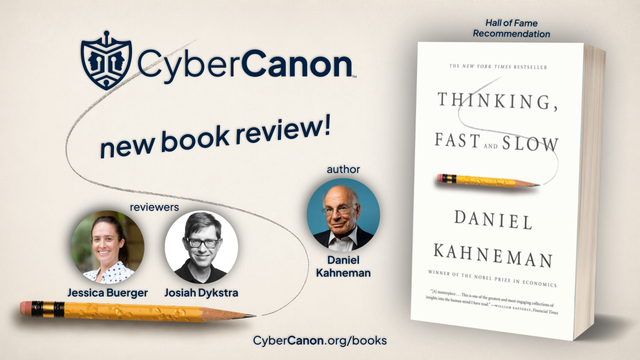
🤔 𝙏𝙝𝙞𝙣𝙠𝙞𝙣𝙜, 𝙁𝙖𝙨𝙩 𝙖𝙣𝙙 𝙎𝙡𝙤𝙬
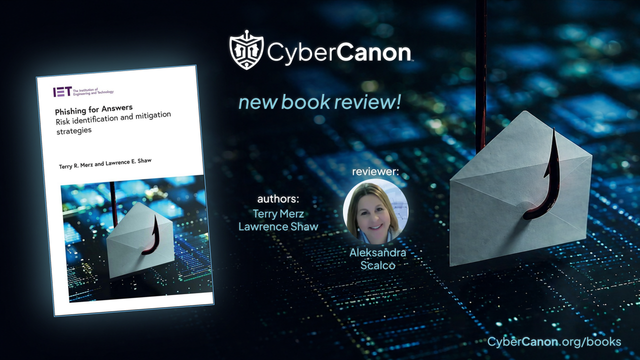
🪝 𝙋𝙝𝙞𝙨𝙝𝙞𝙣𝙜 𝙛𝙤𝙧 𝘼𝙣𝙨𝙬𝙚𝙧𝙨
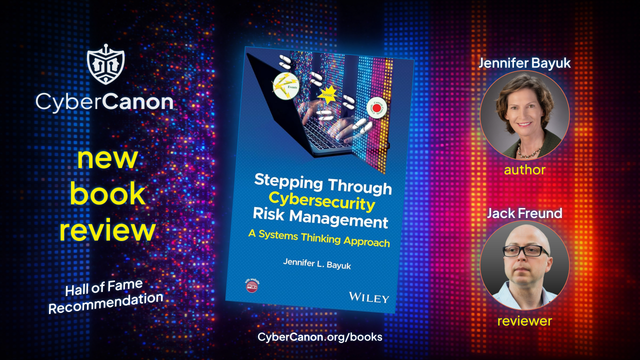
Bookmark https://cybercanon.org/books/ for the most recent reviews.