Alright team, it's been a pretty eventful 24 hours in the cyber world! We've got critical zero-days under active exploitation, several significant breaches, new spyware, and a big debate on national cyber strategy. Let's dive in:
Microsoft SharePoint Zero-Day Under Active Exploitation ⚠️
- A critical remote code execution (RCE) zero-day, CVE-2025-53770 (CVSS 9.8), is being actively exploited in on-premises Microsoft SharePoint servers globally. This flaw is a bypass of a patch for a previous vulnerability (CVE-2025-49706) released in July's Patch Tuesday.
- Attackers, suspected to be nation-state actors, are using an exploit dubbed "ToolShell" to gain unauthenticated access, exfiltrate sensitive data, deploy backdoors, and steal cryptographic machine keys, allowing persistent access even after patching.
- Microsoft has released emergency patches for SharePoint Server 2019 and Subscription Edition, but SharePoint Server 2016 remains unpatched. Organisations with public-facing on-prem SharePoint should assume compromise, investigate for malicious files (e.g., spinstall0.aspx), rotate machine keys, and consider disconnecting servers if immediate patching isn't possible.
🗞️ The Record | https://therecord.media/microsoft-sharepoint-zero-day-vulnerability-exploited-globally
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/microsoft/microsoft-releases-emergency-patches-for-sharepoint-rce-flaws-exploited-in-attacks/
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2025/07/21/infosec_in_brief/
🤫 CyberScoop | https://cyberscoop.com/microsoft-sharepoint-zero-day-attack-spree/
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2025/07/21/massive_security_snafu_microsoft/
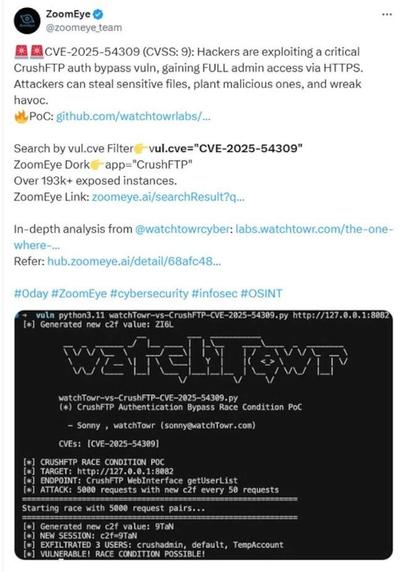
CrushFTP Zero-Day Under Active Exploitation 🛡️
- CrushFTP is warning customers about CVE-2025-54309, a critical zero-day actively exploited since at least July 18th, allowing attackers to gain administrative access to the web interface due to mishandled AS2 validation.
- The vulnerability affects all CrushFTP versions below 10.8.5 and 11.3.4_23. Over 1,000 unpatched instances are exposed online, with some attackers manipulating exploited versions to appear up-to-date.
- Admins should immediately update to the latest versions, review upload/download logs for unusual activity, enable automatic updates, and consider IP whitelisting or using a DMZ instance to mitigate exploitation.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/over-1-000-crushftp-servers-exposed-to-ongoing-hijack-attacks/
🗞️ The Record | https://therecord.media/file-transfer-crushftp-zero-day
Poland Investigates Air Traffic Control Disruption 🚨
- Poland's internal security agency is investigating a temporary outage in the country's air traffic control system that caused widespread flight delays on Saturday, with potential sabotage being scrutinised.
- The outage was attributed to an unspecified technical malfunction, not a cyberattack, but national security services are looking for signs of sabotage given Poland's heightened alert over suspected Russian-linked acts.
- This incident follows previous accusations by Poland against Moscow for "air terror" operations and involvement in a 2023 shopping centre fire, highlighting ongoing hybrid threats in the region.
🗞️ The Record | https://therecord.media/poland-investigates-potential-sabotage-air-traffic-control
Alaska Airlines Grounds Fleet Due to IT Issue ✈️
- Alaska Airlines temporarily grounded its fleet due to an unspecified IT issue, causing significant operational disruption.
- While the nature of the incident is unconfirmed, the Scattered Spider ransomware gang, known for targeting airlines, is an obvious suspect, especially given recent incidents affecting Hawaiian Airlines (owned by Alaska), Qantas, and Air Serbia.
- The airline has apologised for the inconvenience and is working to resolve the issues, advising customers to check flight status before heading to the airport.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2025/07/21/alaska_airlines_it_incident_grounding/
Indian Crypto Exchange CoinDCX Suffers $44M Theft 💰
- Indian cryptocurrency exchange CoinDCX confirmed a theft of over $44 million worth of USDC and USDT from one of its internal operational accounts over the weekend.
- User funds were not impacted as operational accounts are segregated from customer wallets, and CoinDCX is absorbing the losses from its own treasury reserves.
- The company is investigating, patching vulnerabilities, and tracing the stolen funds, offering a bug bounty program and up to 25% of recovered funds for assistance.
🗞️ The Record | https://therecord.media/indian-crypto-dcx-millions-stolen
Dell Product Demo Platform Breached 💻
- Dell confirmed a breach of its "Solution Center" product demonstration platform by a threat actor, but stated that no sensitive customer or partner information was involved.
- The platform is intentionally separated from Dell's main networks and customer systems, and the data contained is primarily synthetic or publicly available test data.
- The WorldLeaks ransomware gang (a revamp of Hunters International) has claimed responsibility for the incident, which Dell says had limited impact.
🗞️ The Record | https://therecord.media/hackers-hit-dell-product-demo-platform-limited-impact
Dior Notifies US Customers of Data Breach 🛍️
- The luxury fashion house Dior is sending data breach notifications to US customers following a cybersecurity incident on January 26, 2025, discovered on May 7, 2025.
- Exposed information includes full names, contact details, physical addresses, dates of birth, and in some cases, passport/government ID numbers and Social Security Numbers. No payment details were compromised.
- This incident is believed to be linked to the ShinyHunters extortion group, which previously breached a third-party vendor affecting other LVMH brands like Louis Vuitton.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/dior-begins-sending-data-breach-notifications-to-us-customers/
Ring Denies Breach Amid Suspicious Login Reports 🏠
- Ring is attributing a surge in suspicious login reports from May 28th to a "backend update bug" that incorrectly displays prior login dates and devices.
- However, many customers are disputing Ring's explanation, reporting unknown devices, strange IP addresses, and countries they've never visited, along with unreceived MFA prompts and live view activity when no one accessed the app.
- Users are advised to review authorized devices in the Control Center, remove unrecognized entries, change passwords, and enable two-factor authentication.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/ring-denies-breach-after-users-report-suspicious-logins/
Arizona Election Website Defaced, CISA Criticised 🗳️
- Arizona election officials reported a hack on a statewide online portal for political candidates, resulting in the defacement of candidate photos with images of the late Iranian Ayatollah Ruhollah Khomeini.
- The attack, which occurred after US bombings of Iranian nuclear sites, involved uploading an image file containing a Base64-encoded PowerShell script to take over the server. Officials believe it was pro-Iranian interests.
- Arizona's Secretary of State criticised CISA, claiming the agency has been "weakened and politicized" under the current administration, leading to a loss of confidence in federal election security support.
🤫 CyberScoop | https://cyberscoop.com/arizona-secretary-of-state-website-hack-candidate-portal-criticizes-cisa/
New Iranian Android Spyware Discovered 📱
- Lookout security researchers have discovered four new samples of DCHSpy Android spyware, linked to the Iranian Ministry of Intelligence and Security (MOIS), surfacing shortly after the Iran-Israel conflict began.
- Disguised as VPN apps (Earth VPN, Comodo VPN), the malware collects WhatsApp data, records audio/video, and exfiltrates sensitive files, indicating continued development and usage by the MuddyWater espionage group.
- The distribution via Telegram channels, sometimes using "Starlink" lures, suggests targeting Iranian dissidents, activists, and journalists, highlighting the MOIS's efforts to surveil citizens.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2025/07/21/muddywaters_android_iran/
ExpressVPN Fixes RDP IP Leak Bug 🔒
- ExpressVPN has patched a flaw in its Windows client (versions 12.97 to 12.101.0.2-beta) that caused Remote Desktop Protocol (RDP) traffic to bypass the VPN tunnel, exposing users' real IP addresses.
- The issue stemmed from debug code mistakenly included in production builds. While encryption wasn't compromised, RDP traffic was visible to observers like ISPs.
- Users are advised to upgrade to version 12.101.0.45 immediately. ExpressVPN states the risk was low for typical consumers as RDP is primarily used by IT admins and enterprises.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/expressvpn-bug-leaked-user-ips-in-remote-desktop-sessions/
US Cyber Posture Shift: From Defense to Offense 🇺🇸
- The US is reportedly shifting its cyber posture towards more robust offensive operations, backed by a proposed $1 billion cyber initiative under the 2026 National Defense Authorization Act (NDAA).
- This pivot is driven by a changing threat landscape where adversaries like China's Volt Typhoon and Russia's campaigns are actively preparing for conflict and disruption, not just espionage.
- The argument is that a defensive-only approach has emboldened adversaries, and a more muscular cyber posture, integrating offensive capabilities with military and intelligence operations, is necessary for deterrence and to impose costs.
🤫 CyberScoop | https://cyberscoop.com/us-offensive-cyber-operations-2025-defense-shift-op-ed/
#CyberSecurity #ThreatIntelligence #ZeroDay #Vulnerability #RCE #SharePoint #CrushFTP #CyberAttack #DataBreach #Ransomware #Spyware #NationState #InfoSec #IncidentResponse #CyberWarfare